Last year, Oregon’s Health CO-OP, a non-profit health insurance company, announced that a stolen laptop compromised the personal information of more than 15,000 current and former members. While an investigation subsequently revealed there was no evidence that the data was used maliciously, the incident created a costly mess for the organization, both financially and from a PR perspective.
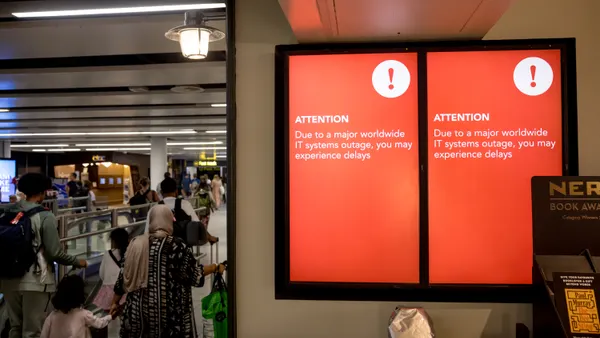
Oregon’s Health CO-OP is certainly not alone. As workers become more mobile, lost corporate laptops and smartphones present a growing enterprise security risk. Some areas face more risk than others.
In San Francisco, for example, recent reports reveal there have been more than 70 car break-ins per day. In many cases, the vandals are after laptops and other technology. Per Gartner's estimates, a laptop is stolen every 53 seconds in the U.S.
This presents a conundrum for businesses. Employees want device access all the time, but that can make data vulnerable. It’s certainly much easier to steal a laptop than hack a corporate database. Today there are more types of mobile devices than ever before and once a mobile device stolen, it’s only a matter of time before thieves figure out how to break in.
"It’s possible to crack every standard Windows password in less than six hours, for less than $800 in parts," said Al Sargent, senior director at OneLogin. "Once a hacker breaks into a laptop, they can easily access all the corporate data stored on it and access any web applications with still active sessions. Gmail, for instance, leaves sessions open for days."
IT leaders are aware of the problem. According to a Citrix/Ponemon Institute survey released in January, more than 70% of IT leaders admit they are at risk from an inability to control employees’ devices. Clearly, more companies need to use the appropriate safeguards to ensure information is protected no matter where it is, or on what device it is accessed.
"What’s most important when looking at mobile security is to ensure that the right identity and access management policies are in place and that those policies are strictly enforced," said Stan Black, CSO at Citrix. "By controlling access, businesses can better control their sensitive business information."
Mobile device management vs. enterprise mobile management
The growing use of mobile devices to conduct business is prompting a spike in demand in the mobile threat defense market. Mobile threat defense companies can provide employees a security app to install on their mobile device, which, according to Gartner, can do things like scan for dangerous apps or risky Wi-Fi networks while workers are on the go, or disable a device if it’s reported stolen. FireEye, Lookout and Better Mobile are among the leaders in the mobile threat defense market to date.
While the MDM market is expected to grow from $1.5 billion in 2016 to $5.5 billion in 2021, it’s also evolving. Because BYOD now accounts for 80% of devices in corporations, many legacy MDM vendors have to rethink their products, said Sargent. That’s because legacy MDM takes over a device, giving IT full control over it, but that’s not always the best solution.
"That might have worked for company-owned devices," said Sargent. "But it doesn’t work for BYOD devices that have massive amounts of irreplaceable personal data and serve as the passport to modern life."
MDM may not be enough anymore as the enterprise mobile environment continues to get messier and more complex, according to Michael Fauscette, chief research officer at G2 Crowd.
"MDM and mobile app management (MAM) used to be two different approaches to trying to solve the same problem," said Fauscette. "Today though, the overall approach is moving to enterprise mobile management suites (EMM), which are a multiple mode approach to the problem."
EMM often includes device management, applications management and content management working together with cloud apps from multiple vendors to provide a more comprehensive approach. But they tend to take a bias from one of the three perspectives, explained Fauscette.
"While some are more device centric, some more applications centric and some focused more on content, all three are important," said Fauscette. "These solutions also must address multiple security scenarios, policy based security, integration, device and OS compatibility, support, containerization — to keep business and personal separate — and administration. Lastly, the solution should be built in such a way that it can adapt to whatever the next hot device might be."
A more mobile future
Whether it’s MDM, EMM or another approach, it’s clear enterprises will need to do more to protect their networks as employees continue to become more mobile. And mobile security does appear to be high on the list of priorities. Approximately 80% of CIOs plan to increase spending on security in 2017, according to the Piper Jaffray 2017 CIO Survey.
In the enterprise, the issue of how to pay for mobile defense solutions can be a sticking point. IT departments are generally not given extra resources for mobile device management, but that could soon change. As hackers become more adept at breaking into mobile devices, companies are looking for ways to better protect themselves, and its likely MDM or EMM funding will soon become more common.
Until then, experts recommend businesses adopt good security practices overall and use a range of precautionary measures to safeguard their organization. At the very least, organizations should enforce complex passwords that are hard to guess and make sure those passwords are regularly changed.
The answer "goes back to access management, having the right policies in place, making sure your business has the right solutions in place to tackle security business challenges and minimize emerging threats," said Black.