When the world plunged into the COVID- 19 pandemic in March 2020, IT was completely unprepared to support thousands of remote and work-from-home employees overnight.
Even so, what they were able to accomplish between March and May of that year was remarkable: IT found a way to keep organizations up and running in a matter of days.
But, with everyone working from home, this meant the tools employees relied on while in the office, like network file sharing, were not as effective when accessed from outside the corporate network. So, employees did what they have always done when IT is unable to provide them with the technology they need, they sourced it themselves.
Even though firm numbers are hard to come by, Gartner estimates content collaboration tools were the main culprit in a surge of shadow IT or rogue IT, depending on which term you prefer.
With the advent of SaaS, shadow IT in the traditional sense, where someone uses things such as personal email to get work done, is actually on the decline, Gartner said.
This is because IT has either already sanctioned a wide array of useful SaaS tools that it does not provide directly, or the business units are asking IT's permission to use a new service before they buy it.
"It's clear that we are moving away from shadow IT in the classic sense and moving into the era of business-led IT where workers are making decisions about what apps they want to use to get their job done," said Lane Severson, senior research director at Gartner. "But they are working with IT to make sure those apps are sanctioned. They aren't just buying random cloud applications and expensing them as much as they were pre-COVID[-19]."
Although he is uncomfortable with the term, the idea of business-led IT has some validity to it, said Rob Zahn, CIO at AAA of Ohio. During the pandemic, everyone was asking for IT's help. Because of that, the incidents of people using unsanctioned apps actually went down in his organization.
Cloud changed the shadow IT equation
Cloud has changed the way CIOs should think about shadow IT, said David Higgins, EMEA technical director at CyberArk, an identity and access management vendor.
The use of cloud adds layers of complexity and risk since many more privileges can be assigned to the average user. In AWS, for example, any user can be assigned upwards of 7,000 different entitlements, he said.
"What we've also seen in our own research is a different term that we're using," he said. "It's not just shadow IT but also this term of 'shadow admin,' which is a consequence of digital transformation and consuming more cloud-based services."
Shadow IT was once solely the domain of sophisticated super-users who had the technical acumen to set up and run infrastructure and applications without IT knowing about. Then came cloud apps like email and file storage solutions that people began to casually use to move files around — again, without IT knowing about it. Both of these are instances of rogue IT.
The former is more common in application development environments and in areas of the organization where a needed tool is too expensive. People will often adopt an open source version to get their jobs done, said Sophat Chev, chief advisor, Security at ConvergeOne, an IT services provider.
"Your biggest hurdle and challenge is going to be accepting what the end user needs as a way of maintaining their contribution to the business," he said.
Business people are more likely to get IT involved early if they believe IT is there to help, not shut them down, according to Lane. "The rogue IT element is mostly still folks trying to get their job done and feeling like working with IT is going to take too long or won't work for their specific solution," he said.
What this means for the CIO and CISO
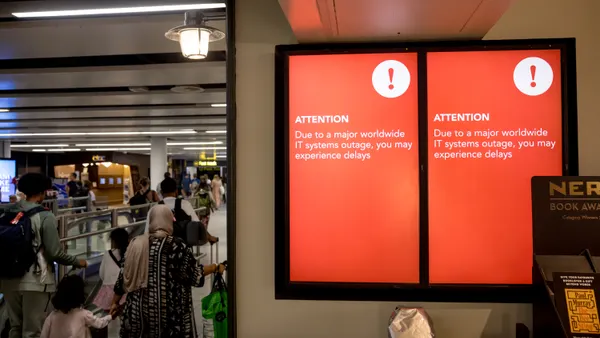
Managing rogue IT is a challenge for CIOs and CISOs for a number of reasons: they don't know what they don't know, cloud providers are savvier than ever at selling directly to end users, and the tools for uncovering shadow IT are not 100% effective.
One-third of companies in the U.S. today are doing an adequate job of keeping rogue IT under control, according to a survey from ManageEngine. But the likelihood of getting shadow IT 100% under IT control is lower than ever, given the ease with which technology can be purchased today and the amount of high-quality freemium apps available.
Aside from running network scanning software and tracking expenses at the departmental level to uncover as many unknown applications and services as possible, Zahn recommends rediscovering the art of communication. Talk to your peers in the organization. Find out what technology they currently run, what they'd like to be running, what their problems are, and the potential technology needs of any projects they are working on.
When CIOs strive to become effective communicators instead of order takers, they will be in a better position to act as guides; helping the organization's leaders make good technology decisions that avoid unnecessary risk, add to technical debt, or create application and infrastructure redundancies.
"The CIO, more than ever, just needs to be out among his peers talking to them on a regular basis," he said, "so that you're keeping aware of the type of things that they're doing, forming that relationship."