Dive Brief:
- Bad actors are incrementally publishing breached data online from manufacturer Visser Precision, Brett Callow, threat analyst at Emsisoft, told CIO Dive. Some of the published data belongs to Visser customers including Tesla, SpaceX, Boeing and Lockheed Martin.
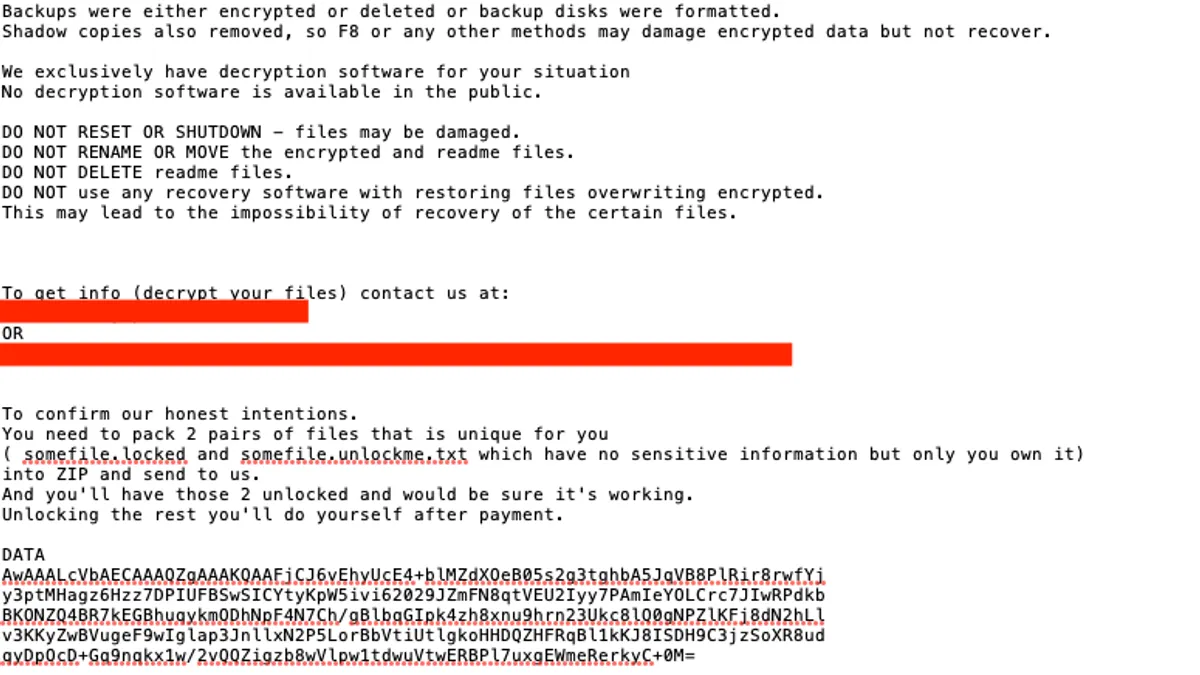
- The manufacturer, hit by ransomware DoppelPaymer, encrypts and steals data. The leaked data includes non-disclosure agreements and proprietary data.
- Visser Precision was a "target of a criminal cybersecurity incident, including access to or theft of data. The company continues its comprehensive investigation of the attack, and business is operating normally," a Visser spokesperson told CIO Dive in an email. The supplier "will make no further press comment at this time."
Dive Insight:
DoppelPaymer is similar to Maze, a ransomware strain that encrypts and exfiltrates data.
Maze famously targeted Pensacola, Florida, interrupting services for the city. In January, cable manufacturer Southwire filed a lawsuit against Maze's John Doe hackers for publishing its data online.
And like Maze, the operators behind DoppelPaymer are threatening further publication if the ransom goes unpaid.
Anyone with internet access can see the exfiltrated documents from Visser Precision, according to Callow. Visser Precision's cyberattack impacts its business partners, a favorable attack style among bad actors.
Quest Diagnostics and LabCorp's billing collector was breached in 2019, compromising millions of patient records. In 2017, Notpetya leveraged software in the supply chain to infect and spread through an update.
Ransomware collectively kills existing protocols to supersede control of a system. Known ransomware strains are detectable by their signatures whereas unknown ransomware is detected by its behavior, according to Callow.
While the circumstances and point of entry in Visser Precision's cyberattack is still under investigation, researchers know that for a ransomware to succeed, it has to evade detection. "One of the ways that can be achieved is by exploiting vulnerabilities such as CVE-2018-19320 to remove or disable security applications," said Callow.