On Mother's Day weekend last year, the world was hit with a real matriarch of malware. So while companies have had a year to dry their tears, revisiting the chaos WannaCry brought to the world may make them reach for another Kleenex.
WannaCry led the way; Nyetya, or NotPetya, hit the tech community about one month later. But before Nyetya could wreak havoc WannaCry hit about 200,000 computers in at least 150 countries.
So who left the door open? Anyone who failed to update Windows 7 systems, despite updates from Microsoft.
One year later, CIO Dive spoke with four cybersecurity experts to get their thoughts on WannaCry and what to expect, if anything, this weekend. Here's what they had to say:
1. Steve Martino, VP and CISO for Information Security at Cisco
Cisco's WannaCry survival boiled down to "operational discipline," and this stems from how Cisco's internal security functions on a regular basis, according to Martino.
As CISO, Martino and his team are tasked with securely enabling the organization. But instead of taking an entirely defensive approach to cybersecurity, Martino said security should be addressed at the cultural level.
If security is intertwined in a company's culture, it can become a series of "trade offs." This will leave room for responsible risk and offer benefits without sacrificing security in the process.
For CISOs, no malware like WannaCry can just "fall off the radar," otherwise a system will get hacked, according to Martino. Instead, CISOs need to be "mindful of how it morphs" to accommodate the security needs of a malware's different strains.
As for an anniversary attack, Martino said "WannaCry isn't done." The strain persists, which was made clear in March after Boeing suffered a WannaCry infection. The original strain is still active, though variants are also typical.
Cisco avoided the attack by distributing patches as soon as Microsoft posted its bulletin. But Martino partially credits luck for playing a hand because the company's server updates were completed the weekend before WannaCry went nuclear.
If anything, Martino found the event "an empowering moment because it had the visibility to help galvanize what we need as a security team," thus escalating the culture of security.
2. Matt Cauthorn, VP of security at ExtraHop
WannaCry initially took advantage of systems that were "not accommodating to software to upgrade," said Cauthorn. These systems include legacy machines in hospitals that make software updates near impossible and WannaCry fed off outdated systems.
But before WannaCry could thrive, it needed an entry point the leaked NSA EternalBlue exploit allowed. EternalBlue changed the nature of hacking because it elevated any hacker's access and it no longer takes a nation state actor to pull off mass hysteria. Because of the leaked exploit, the "stakes are very high," said Cauthorn.
The WannaCry hackers controlled a victim's computer until they paid a ransom and it demonstrated a graduation to a more sophisticated form of kiddie scripts, according to Cauthorn.
It's hard not to breathe a little heavier on the anniversary of a malware attack. As for a potential anniversary attack this weekend, Cauthorn said he "wouldn't bet against it." WannaCry elicited a change in hacker mentality, a shift from disruption to control. When an anniversary arises, security is usually seen bulking up because a threat becomes "very topical and front of mind," said Cauthorn.
It's only a possibility the tech industry learned its lesson from WannaCry last year, Cauthorn said. However, at the very least organizations have gained a greater awareness of "entrenched dependencies [on] specific software or technology approaches" and how they expose companies to further risk.
3. Neill Feather, CEO of SiteLock
Feather is skeptical about an anniversary-style attack. Instead, hackers, like any other type of criminal, prefer to strike when the best opportunity arises. Waiting to attack a year on from WannaCry tends "not to be as meaningful," he said.
SiteLock aids small to medium-sized businesses in malware discovery on their websites, but because these types of businesses often assume malware attacks target larger corporations, security can lag. Hackers take advantage of an available vulnerability, no matter who it belongs to.
Companies of all sizes need accurate insight into what software is in their systems. But Feather warns that something "will always slip through the cracks" if this type of inventory is done manually. Automation is necessary for assigning patches where they are needed.
Organizations resistant to patches may blame the "operational cost" behind the process, said Feather. Not only do updates take time and manpower, they also could impact overall functionality somewhere else in a system, including breaking plugins and integrations.
But Feather advises organizations to never underestimate its level of risk.
"Many businesses underestimate the risk to themselves" because they primarily see attacks on organizations "who look less like their business." WannaCry didn't discriminate against its victims so businesses shouldn't do the same with malware protections.
4. Mounir Hahad, head of Juniper Threat Labs at Juniper Networks
When it comes to heightening security standards on a malware's anniversary, Hahad said there are simply too many attack anniversaries to keep track, in an email to CIO Dive. There is always the desire to expand defense measures on an anniversary, but cyberattacks by nature are unpredictable.
While new defenses should have been added to a network almost immediately after a global cyberattack, there will always be a "trailing crowd that is unable to change its security posture," said Hahad. Unfortunately, organizations can become security laggards from a lack of talent, manual processes or "complex policies."
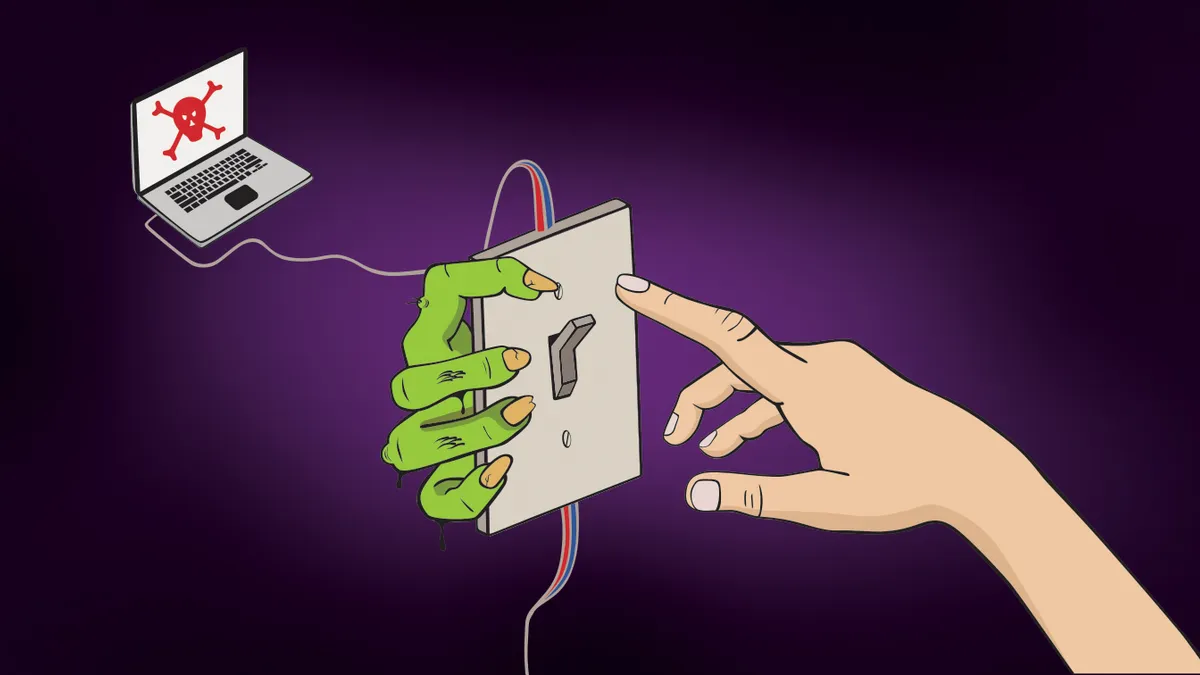
As for the kill switch that ultimately helped take down WannaCry, Hadad admits that kill switches are more often "an exception than a rule," which offers no clear reassurance of the presence of another one in a future attack.