Dive Brief:
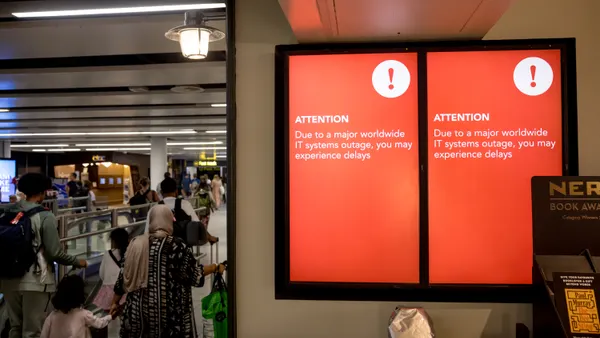
- The number of organizations hit by Friday's massive global "WannaCry" cyberattack reached 200,000 targets in at least 150 countries, the head of the European Union's police agency reported, according to Al Jazeera. The attack disrupted at least 16 hospitals in England as well as large international companies including FedEx, telecom companies Telefónica of Spain and Megafon of Russia and car maker Nissan. Russia's Interior Ministry and several Chinese universities were also affected.
- The malware spread because of flaws in old versions of Windows originally identified by the NSA to hack into PCs before being made public by the Shadow Brokers group in April. The attack prompted Microsoft to take what the company called a "highly unusual" step to provide patches for older versions of Windows that it no longer supports, including Windows XP, Windows 8, and Windows Server 2003, according to The Verge.
- It appears the people behind that attack, who have not yet been identified, earned about $26,000, reports Krebs on Security. The attacks were allegedly slowed when an unidentified 22-year-old computer security expert from Britain accidently found and activated a "kill switch." The expert warns that this attack is not over.
Dive Insight:
It's believed to be the biggest recorded cyberattack of its kind and it may not be over yet. Experts warn that as people return to work Monday, they could start WannaCry up again.
While security experts have warned for years that a massive global cyberattack was possible. WannaCry demonstrated how sophisticated these attacks have become. Rather than infect one PC at a time, WannaCry propagates across entire networks.
It's yet another example of how important it is to update software. Windows 10 is generally regarded as the most secure Windows software available, but until a company migrates away from older versions of Windows to Windows 10, all that security doesn't do much good. Reports have found businesses have been slow to update to Windows 10, but this attack may motivate them.
Europe and Russia were hit the hardest. By Friday evening, the ransomware had spread to the United States and South America, but by that time workers were either gone for the day or were given warnings that allowed the attack to slow.
The attack also proves how potentially dangerous massive computer disruptions can be. At the U.K.'s National Health Service, operations were canceled, critical data was unavailable and phones did not work.